CISCO
STUDY GUIDE
Building Scalable
Cisco Networks (BSCN)
Exam 640-503
Edition 2
www.testkiller.com
Congratulations!!
You have purchased a Testkiller, Ltd Study Guide.
This study guide is a selection of questions and answers similar to the ones you
will find on the official CCNP 640-503 exam. Study and memorize the following
concepts, questions and answers for approximately 15 to 20 hours and you will be
prepared to take the exams. We guarantee it!
Remember, average study time is 15 to 20 hours and then you are ready!!!
GOOD LUCK!
DISCLAIMER
This study guide and/or material is not sponsored by, endorsed by or affiliated with Cisco Sys-
tems, Inc. Cisco®, Cisco Systems®, CCDA™, CCNA™, CCDP™, CCNP™, CCIE™, CCSI™,
the Cisco Systems logo and the CCIE logo are trademarks or registered trademarks of Cisco Sys-
tems, Inc. in the United States and certain other countries. All other trademarks are trademarks
of their respective owners
.
Guarantee
If you use this study guide correctly and still fail the exam, send your official score
notice and mailing address to:
Testkiller, Ltd
8200 Pat Booker Rd. #368
San Antonio, TX 78233
We will gladly refund the cost of this study guide. However, you will not need this
guarantee if you follow the above instructions.
This material is protected by copyright law and international treaties. Unauthor-
ized reproduction or distribution of this material, or any portion thereof, may re-
sult in severe civil and criminal penalties, and will be prosecuted to the maximum
extent possible under law.
Copyright 2001 Testkiller, Ltd. All Rights Reserved.
www.testkiller.com
Table of Contents
Routing Principles........................................................................................................................... 1
Routing Metric............................................................................................................................ 1
RIP Routing Metrics ............................................................................................................... 1
IGRP Routing Metrics ............................................................................................................ 1
Classful Routes ....................................................................................................................... 1
Classless Routing.................................................................................................................... 1
Distance Vector Operation...................................................................................................... 1
Convergence ............................................................................................................................... 1
EIGRP Convergence............................................................................................................... 1
OSPF Convergence................................................................................................................. 2
IP Addresses.................................................................................................................................... 2
Current challenges in IP Addressing........................................................................................... 2
IP Addressing Solutions.............................................................................................................. 2
Hierarchical Addressing.......................................................................................................... 2
Variable Length Subnet Masks............................................................................................... 2
Route Summarization.............................................................................................................. 2
CIDR ....................................................................................................................................... 3
Redistribution Implementation Guidelines ............................................................................. 3
NAT ........................................................................................................................................ 3
Using IP Unnumbered Serial Interface ....................................................................................... 3
Server Location........................................................................................................................... 3
OSPF ............................................................................................................................................... 3
Configuring OSPF in a Single Area............................................................................................ 3
OSPF Operation in a Broadcast Multiaccess Topology ......................................................... 4
OSPF Startup .......................................................................................................................... 4
OSPF over NBMA Topology ................................................................................................. 4
NBMA Mode Neighborship ................................................................................................... 5
Point-to-Multipoint Mode Neighborship ................................................................................ 5
Interconnecting Multiple OSPF Areas........................................................................................ 5
Multiple OSPF Areas.............................................................................................................. 5
Types of Routers..................................................................................................................... 6
Types of Areas ........................................................................................................................ 6
Supporting Route Summarization........................................................................................... 6
EIGRP ............................................................................................................................................. 6
Configuring EIGRP .................................................................................................................... 6
EIGRP Operation.................................................................................................................... 6
EIGRP Packets........................................................................................................................ 6
EIGRP Reliability ................................................................................................................... 7
Topology Table....................................................................................................................... 7
Configuring EIGRP ................................................................................................................ 7
EIGRP Load Balancing........................................................................................................... 7
EIGRP and WAN Links.......................................................................................................... 7
EIGRP Link Utilization .......................................................................................................... 7

www.testkiller.com
Using EIGRP in a Scalable Network...................................................................................... 7
BGP................................................................................................................................................. 8
Configuring Basic Border Gateway Protocol ............................................................................. 8
BGP Use.................................................................................................................................. 8
When to use BGP.................................................................................................................... 8
When not to use BGP.............................................................................................................. 8
BGP Peers or Neighbors ......................................................................................................... 8
Policy-Based Routing ............................................................................................................. 8
Well Known Attributes........................................................................................................... 8
Optional Attributes.................................................................................................................. 9
Defined BGP Attributes.......................................................................................................... 9
BGP Synchronization.............................................................................................................. 9
BGP Message Types ............................................................................................................... 9
Implementing BGP in Scalable Networks ................................................................................ 10
Route Reflectors.................................................................................................................... 10
Policy Control and Prefix Lists............................................................................................. 10
Optimizing Routing Update Operation......................................................................................... 10
Redistribution............................................................................................................................ 10
Policy-based Routing................................................................................................................ 10
Calculating cost for external routes .......................................................................................... 10

www.testkiller.com
GFI - Security & Communication tools for NT/2000: FAXmaker fax server software, Mail essentials email content checking &
anti-virus software and LANguard network security software.
http://www.gfi.com/tt.shtml
1
Key Concepts
Building Scalable Cisco Networks (BSCN)
Routing Principles
Routing is a relay process in which items are forwarded from one location to another. The
mechanism of learning and maintaining awareness of the network topology is considered to be
the routing function.
Routing Metric
In a routed network the routing process relies on the routing protocol to maintain a loop-free to-
pology and to locate the best path to every destination network.
RIP Routing Metrics
RIP is a commonly used routing protocol in small to medium sized TCP/IP networks.
IGRP Routing Metrics
Cisco’s IGRP is a commonly used routing protocol in medium to large sized TCP/IP networks.
IGRP uses a composite metric, based upon bandwidth, delay, reliability, load, and maximum
transmission unit (MTU).
Classful Routes
Classful routing protocols, such as RIPv1 and IGRP, exchange routes to subnetworks within the
same major Class (A, B or C) network. Classful routing is the result of subnet masks not being
included in the routing advertisements generated by most distance vector routing protocols.
Classless Routing
Classless routing protocols can be considered second-generation protocols because they are de-
signed to deal with some of the limitations of the earlier classful protocols.
Distance Vector Operation
The periodic routine routing updates generated by most distance vector routing protocols go only
to directly connected routing devices.
Convergence
In a routed network, the routing process in each router must maintain a loop-free single path to
each possible destination logical network. When all the routing tables are synchronized and each
contains a usable route to each destination network, the network is converged.
EIGRP Convergence
A router running EIGRP uses reliable multicast messages when it sends queries and updates to
other routers.

www.testkiller.com
GFI - Security & Communication tools for NT/2000: FAXmaker fax server software, Mail essentials email content checking &
anti-virus software and LANguard network security software.
http://www.gfi.com/tt.shtml
2
OSPF Convergence
A router running OSPF uses a multicast address to propagate LSAs. LSA is state information
about a link or a network.
IP Addresses
Current challenges in IP Addressing
An IP address consists of a 32-bit number with two components: a network address and a node.
The incredible growth of the Internet has resulted in following challenges:
• IP address exhaustion
• Routing table growth and manageability
IP Addressing Solutions
Solutions have been developed to slow the depletion of IP addresses and to reduce the number of
Internet route table entries by enabling more hierarchical layers in an IP address. These solutions
include the following:
• Subnet masking
• Address allocation for private internets
• Network Address Translation (NAT)
• Hierarchical addressing
• Variable-length subnet masks (VLSMs)
• Route summarization
• Classless Interdomain Routing (CIDR)
Hierarchical Addressing
The benefits of hierarchical addressing are:
• Reduced number of routing table entries
• Efficient allocation of addresses
Variable Length Subnet Masks
The VLSMs are commonly used to maximize the number of possible addresses available for a
network. The benefits if VLSMs are:
• Even more efficient use of IP addresses
• Greater capability to use route summarization
Route Summarization
Route summarization can reduce the number of routes that a router must maintain because it is a
method of representing a series of network numbers in a single summary address.

www.testkiller.com
GFI - Security & Communication tools for NT/2000: FAXmaker fax server software, Mail essentials email content checking &
anti-virus software and LANguard network security software.
http://www.gfi.com/tt.shtml
3
Cisco routers manage route summarization in two ways:
• Sending route summaries
• Selecting routes from route summaries
CIDR
CIDR is a mechanism developed to help alleviate the problem of exhaustion of IP addresses and
growth of routing tables.
Redistribution Implementation Guidelines
• Be familiar with your network and your network traffic
• Do not overlap routing protocols
• One-way redistribution
• Two-way redistribution
NAT
Network Address Translation can be used to merge two large networks without having to re-
address the whole network. Another function of NAT is overloading inside global addresses.
This process allows several inside addresses to use a single IP address. NAT can also use a pool
of addresses or multiple interfaces.
Using IP Unnumbered Serial Interface
To enable IP processing on a serial interface without assigning an explicit IP address to the inter-
face, use the ip unnumbered type number interface configuration command. In the command
type number indicates the type and number of another interface on which the router has an as-
signed IP address.
Server Location
The server location is located in several ways:
• A single server on a single remote medium
• Multiple servers on a single remote medium, sometimes called a server farm
• Multiple servers on multiple remote media
OSPF
Configuring OSPF in a Single Area
OSPF is a link-state technology, as opposed to a distance vector technology such as Routing In-
formation Protocol (RIP). The OSPF protocol performs the two primary functions of every rout-
ing protocol algorithm: path selection and path switching.
The OSPF addresses the following issues:

www.testkiller.com
GFI - Security & Communication tools for NT/2000: FAXmaker fax server software, Mail essentials email content checking &
anti-virus software and LANguard network security software.
http://www.gfi.com/tt.shtml
4
• Speed of convergence
• Support for variable-length subnet masks (VLSMs)
• Network Reachability
• Use of bandwidth
• Method for path selection
Topologies found in OSPF are:
• Broadcast multiaccess topologies
• Point-to-point topologies
• Nonbroadcast multiaccess (NBMA) topologies
OSPF Operation in a Broadcast Multiaccess Topology
Because OSPF topology is dependent on the status of a link between two routers, neighbor
routers must recognize each other on the network before they can share information. This proc-
ess is done using the Hello Protocol. The information contained in a Hello Packet is as follows:
• Router ID
• Hello and dead intervals
• Neighbors
• Area-ID
• Router priority
• DR and BDR IP address
• Authentication password
• Stub area flag
The DR and BDR add value to the network in the following ways:
• Reducing routing update traffic
• Managing link-state synchronization
OSPF Startup
The steps involved when routers running OSPF come up on a network.
1. Exchange Process
2. Discovering Routes
OSPF over NBMA Topology
OSPF runs in two official modes in NBMA topologies:
• Nonbroadcast Multiaccess (NBMA)
• Point-to-Multipoint

www.testkiller.com
GFI - Security & Communication tools for NT/2000: FAXmaker fax server software, Mail essentials email content checking &
anti-virus software and LANguard network security software.
http://www.gfi.com/tt.shtml
5
NBMA Mode Neighborship
Consider the following before using this mode:
• Full mesh and direct communication
• Stability of the network
Point-to-Multipoint Mode Neighborship
This mode has the following properties.
• Does not require a fully meshed network
• Does not require static neighbor configuration
• Uses one IP subnet
• Duplicates LSA packets
Configuring OSPF over NBMA Topology
• RFC –compliant Modes
NBMA Mode
Point-to-multipoint Mode
• Cisco-defined Modes
Point-to-multipoint nonbroadcast mode
Broadcast mode
Point-to-point mode
Interconnecting Multiple OSPF Areas
Multiple OSPF Areas
The following areas need to be addresses.
Frequent calculations of the shortest path first (SPF) algorithm
Large routing table
Large link-state table
The hierarchical topology of OSPF has the following advantages.
Reduced frequency of SPF calculations
Smaller routing tables
Reduced link-state update (LSU) overhead

www.testkiller.com
GFI - Security & Communication tools for NT/2000: FAXmaker fax server software, Mail essentials email content checking &
anti-virus software and LANguard network security software.
http://www.gfi.com/tt.shtml
6
Types of Routers
1. Internal Router
2. Backbone Router
3. Area Border Router
4. Autonomous System Boundary Router (ASBR)
Types of Areas
The characteristics that you assign an area control the type of route information that it receives.
The possible area types include the following.
Standard area
Backbone area
Stub area
Totally stubby area
Not-so-stubby area
Supporting Route Summarization
Summarization is the consolidation of multiple routes into a single advertisement. With summa-
rization, only summarized routes will propagate into the backbone. Two types of summarization
exist, as follows:
1. Interarea route summarization
2. External route summarization
EIGRP
Configuring EIGRP
EIGRP is a Cisco owned protocol that combines the advantages of link-state and distance vector
routing protocols. This hybrid protocol has the following features:
Rapid convergence
Reduced bandwidth usage
Multiple network layer support
EIGRP Operation
Elements of EIGRP operation are:
EIGRP Packets
EIGRP neighbor relationship
EIGRP Packets
EIGRP uses the following five types of packets:

www.testkiller.com
GFI - Security & Communication tools for NT/2000: FAXmaker fax server software, Mail essentials email content checking &
anti-virus software and LANguard network security software.
http://www.gfi.com/tt.shtml
7
Hello
Update
Queries
Replies
ACK
EIGRP Reliability
EIGRPs reliability mechanism ensures delivery of critical route information to neighboring
routers. This information is required to allow EIGRP to maintain a loop-free topology. All pack-
ets carrying routing information are sent reliably.
Topology Table
When the router dynamically discovers a new neighbor, it sends an update about the routes that it
knows to its new neighbor and receives the same from the new neighbor. These updates populate
what is known as the Topology Table.
Configuring EIGRP
Perform the following steps to configure EIGRP for IP.
1. Enable EIGRP and define the autonomous system.
2. Indicate which networks are parts of the EIGRP autonomous system.
3. If using serial links especially for the frame relay or SMD define the bandwidth of a link
for the purpose of sending routing update traffic on the link.
EIGRP Load Balancing
Load balancing is the capability of a router to distribute the traffic over all its network ports that
are the same distance from the destination address.
EIGRP and WAN Links
EIGRP is scalable on both point-to-point links and NBMA multipoint and point-to-point links. A
solid understanding of EIGRP operation coupled with knowledge of link speeds can yield an ef-
ficient, reliable and scalable router configuration.
EIGRP Link Utilization
By default EIGRP will use up to 50 percent of the bandwidth declared on an interface or subin-
terface. This percentage can be adjusted.
Using EIGRP in a Scalable Network
The following are some of the many variables that impact network scalability.
The amount of information exchanged between neighbors
A topology change
The depth of topology
The number of alternative paths through the network

www.testkiller.com
GFI - Security & Communication tools for NT/2000: FAXmaker fax server software, Mail essentials email content checking &
anti-virus software and LANguard network security software.
http://www.gfi.com/tt.shtml
8
BGP
Configuring Basic Border Gateway Protocol
BGP is an interdomain routing protocol also known as an EGP.
Two types of routing protocols are as follows:
Interior Gateway Protocol (IGP)
Exterior Gateway Protocol (EGP)
BGP Use
BGP is used between autonomous systems. The main goal of BGP is to provide an interdomain
routing system that guarantees the loop-free exchange of routing information between two
autonomous systems. BGP routers exchange information about paths to destination network.
When to use BGP
Use when one of the following conditions exists.
The AS allows packets to transit through it to reach other autonomous systems.
The AS has multiple connections to other autonomous systems.
The flow of traffic entering and leaving the AS must be manipulated.
When not to use BGP
Do not use BGP when one or more of the following conditions exist.
A single connection to the Internet or another AS.
No concern for routing policy and route selection.
Lack of memory or processor power on routers to handle constant BGP updates.
A limited understanding of route filtering and BGP path selection process.
Low bandwidth between autonomous systems.
BGP Peers or Neighbors
Any two routers that have found a TCP connection to exchange BGP routing information are
called peers or neighbors.
Policy-Based Routing
BGP allows policy decisions at the AS level to be enforced. This setting of policies or rules for
routing is known as policy-based routing.
Well Known Attributes
A well-known attribute is one that all BGP implementations must recognize. These attributes are
propagated to BGP neighbors.
www.testkiller.com
GFI - Security & Communication tools for NT/2000: FAXmaker fax server software, Mail essentials email content checking &
anti-virus software and LANguard network security software.
http://www.gfi.com/tt.shtml
9
Optional Attributes
An optional attribute need not be supported by all BGP implementations; it could be a private
attribute.
Defined BGP Attributes
The attribute defined by BGP includes the following.
Well-known, Mandatory Attributes:
• AS-path
• Next-hop
• Origin
Well-known, Discretionary Attributes:
• Local preference
• Atomic Aggregate
Optional, Transitive Attribute;
• Aggregator
• Community
Optional, Nontransitive Attribute;
• Multi-exit-discriminator (MED)
BGP Synchronization
The BGP synchronization rule states that a BGP router should not use or advertise to an external
neighbor a route learned by IBGP, unless that route is local or is learned from the IGP.
BGP Message Types
BGP defines the following message types:
• Open
• Keepalive
• Update
• Notification
An open message includes the following information:
• Version
• My autonomous system
• Hold time
• BGP identifier (router ID)
• Optional parameters
An update message may include the following fields.
www.testkiller.com
GFI - Security & Communication tools for NT/2000: FAXmaker fax server software, Mail essentials email content checking &
anti-virus software and LANguard network security software.
http://www.gfi.com/tt.shtml
10
• Withdrawn routes
• Path attributes
• Network layer reachability information
Implementing BGP in Scalable Networks
Route Reflectors
Route reflectors modify the BGP split horizon rule by allowing the router configured as the route
reflector to propagate routes learned by IBGP to other IBGP peers. The route reflector will have
a partial IBGP peering with other routers, which are called clients.
Policy Control and Prefix Lists
The advantages of using prefix lists are as follows:
• A significant performance improvement over access list in loading and route lookup of
large lists.
• Support for incremental modifications.
Optimizing Routing Update Operation
Redistribution
Cisco routers allow internetworks using different routing protocols to exchange routing informa-
tion though a feature called route distribution.
Redistribution Considerations:
• Routing feedback (loops)
• Incompatible routing information
• Inconsistent convergence time
Policy-based Routing
The benefits that can be achieved by implementing policy based routing in networks include the
following.
• Source-based transit provider selection
• Quality of service
• Cost savings
• Load sharing
Calculating cost for external routes
You can configure the router to generate the following external packet types (the cost depends on
the external type):

www.testkiller.com
GFI - Security & Communication tools for NT/2000: FAXmaker fax server software, Mail essentials email content checking &
anti-virus software and LANguard network security software.
http://www.gfi.com/tt.shtml
11
• Type-1 (E1) - The metric is calculated by adding the external cost to the internal cost of
each link the packet crosses.
• Type-2 (E2) - The packet will always have the external cost assigned, no matter where in
the area it crosses. (Type-2 routes are preferred unless two equal cost routes exist).
After receiving the updates, routers add updates to their link-state databases and recalculate the
tables in the following order:
1. Type-1 and Type-2 LSAs. Calculate the paths to destinations within their area and add
these entries into the routing table.
2. Type-3 and Type-4 LSAs (inter-area rout entries). Calculate the paths to the other areas
within the internetwork. Intra-area route destinations are kept over inter-area routes.
3. Type-5 destinations. All routers, except those that are in a form of stub area, then calcu-
late the paths to the AS external destinations.

www.testkiller.com
GFI - Security & Communication tools for NT/2000: FAXmaker fax server software, Mail essentials email content checking &
anti-virus software and LANguard network security software.
http://www.gfi.com/tt.shtml
12
WARNING: It is important that you read and study the
“CCNP Keypoints” portion of this study guide. We have iden-
tified important “KEYPOINTS” in this section. Please ensure
that you absolutely know and understand these prior to sitting
for the exam.
www.testkiller.com
GFI - Security & Communication tools for NT/2000: FAXmaker fax server software, Mail essentials email content checking &
anti-virus software and LANguard network security software.
http://www.gfi.com/tt.shtml
13
Keypoints to Remember
1.
When configuring serial 0 for OSPF in a point-to-point mode using subinterfaces, the
first command will always be very similar to this:
interface serial 0.1.-2-.
2. Use
the
show ip ospf interface command to verify that OSPF interfaces are configured
in the proper area and to display neighbor adjacencies.
3.
OSPF is always better than RIPv.1 in a large network. OSPF has virtually no limitations
on reach and supports variable length subnet masks.
4.
When configuring OSPF Ethernet, you will always enter the commands in the following
order:
interface Ethernet 0
IP address <network number> <subnet mask>
!
interface Ethernet 1
IP address <network number> <subnet mask>
!
router ospf <number>
network <number> area <number>
network <number> area <number>
5.
Once the OSPF routing process is enabled, the following command will select only the
router’s network interfaces to participate in an OSPF area:
Network <number> <wildcard mask> area <number>
6.
OSPF can support variable length subnet mask (VLSM) because OSPF carries subnet
mask confirmation in the link advertisements.
7. Use
the traceroute command to view routing tables and determine if a router is using the
best path to forward packets on a specific network.
8.
Route summarization uses hierarchical routing to allow one route update to represent
many downstream networks.
9.
The following are true about BGP:

www.testkiller.com
GFI - Security & Communication tools for NT/2000: FAXmaker fax server software, Mail essentials email content checking &
anti-virus software and LANguard network security software.
http://www.gfi.com/tt.shtml
14
Periodic keepalives are sent to verify TCP connectivity.
Reliability comes from using TCP port 179 as its transport.
Topology awareness is kept current by routine periodic update.
BGP based routing allows policy decisions at the AS level to be enforced.
BGP allows an AS to send traffic to a neighboring AS intending that the traffic
take a different route than from the traffic originating in the neighboring AS.
BGP can only advertise routers that it uses to be its peers in other autonomous
systems.
10.
VLSM allows a way of controlling the number of reliable hosts on the network by ma-
nipulating the mask in an attempt to efficiently allocate IP addresses.
11.
Neighbors or peers are created when two BGP routers form a transport protocol connec-
tion between each other. Each router running BGP is a called a BGP speaker.
12.
By default, the next hop attribute advertised by EBGP is carried into IBGP.
13.
The “default-information originate always” command is required whenever you want to
propagate a default route into an OSPF autonomous system.
14.
BGP communities allow routers to filter incoming or outgoing updates. They are indica-
tors used by routers to allow other routers to make decisions based upon these indicators.
15.
An autonomous system is a set of routers under a single technical administration. It uses
EGP to route packets to other autonomous systems and IGP or multiple IGPs to route
packets within the autonomous system.
16.
Routers running EBGP are usually directly connected. They need to be able to reach
each other.
17.
An EIGRP router determines when a neighbor is unavailable according to when the hold
time is exceeded.
18.
Routers run EBGP in order to exchange BGP information with routers in other autono-
mous systems.
19.
There are three basic elements that are required for a router to be able to forward a
packet:
1.
The best route
2. Destination
address
3.
Summarized routes entry

www.testkiller.com
GFI - Security & Communication tools for NT/2000: FAXmaker fax server software, Mail essentials email content checking &
anti-virus software and LANguard network security software.
http://www.gfi.com/tt.shtml
15
20.
RIPv.1 routing updates do not support VLSM because they do not contain the subnet
mask.
21.
In a routing entry table, the time value represents an incrementing router indicating how
long the router has been in the table since the last update.
22.
All learned router entries are kept in an EIGRP routing table.
23.
When configuring EIGRP for NBMA operation, the purpose of IP bandwidth-percentage
EIGRP command is to adjust the percent of bandwidths that EIGRP packets can use on
an individual router interface.
24.
A router running BGP with all the default settings will not use a route learned by IBGP
unless that route is learned from IGP. Also it will not advertise a route learned by IBGP
to an external neighbor unless that route is learned from IGP.
25. Redistributing
dynamic
routes by the BGP method of sending route information into BGP
routing protocol is not recommended.
26. The neighbor ip-addr | peer-group-name weight <weight-value> command is used to
change the BGP weight attribute of updates coming from a neighbor router.
27.
Many BGP sessions may be created, and a significant amount of bandwidth may be taken
on slow WAN links when a full event mesh of BGP sessions is configured within an
autonomous system.
28.
An autonomous system connected via BGP to more than one ISP is referred to as Multi-
homed.
29.
The following three IP protocols support variable length subnet masks (VLSM):
1. RIPv.2
2. OSPF
3. EIGRP
30.
In an OSPF area will no longer exchange information with other routers in the area once
you configure an ABR as a stub, and the area is a transit area for virtual links.
31.
A metric is a routing table entry, which is used to indicate the best route to reach a desti-
nation network.
32.
The show controller command will allow you to determine whether a serial interface is
connected to a DTE or DCE cable.

www.testkiller.com
GFI - Security & Communication tools for NT/2000: FAXmaker fax server software, Mail essentials email content checking &
anti-virus software and LANguard network security software.
http://www.gfi.com/tt.shtml
16
33.
Link state routing determines path by bandwidth-based values. It sends updates rather
than complete routing tables when a network change occurs.
34.
Variable length subnet masks have a greater capability to use route summarization.
VLSMs allow for more hierarchical levels within an addressing plan.
35.
In a multiarea OSPF network, all areas that incorporate NBMA topology must be full
mesh, and cannot be configured as stub areas.
36.
Variable length subnet masking supports hierarchical addressing. It is specifically used
in the IP environment.
37.
In a multipoint WAN topology using EIGRP on a serial interface, you should configure
the bandwidth by multiplying the number of circuits by CIRs provisioned for each circuit
in the topology.
38. The
show ip route eigrp (process-id)
command displays only the current EIGRP entries
in the routing table.
39.
When using routes with EIGRP route selection, the cost between the local router and the
destination is a feasible distance.
40.
An EIGRP router discovers its neighbors when it receives acknowledgements for the
transmitted hello packets.
41. The
no auto summary command is used to turn off automatic summarization for EIGRP
routes.
42.
The route summarization feature in EIGRP enables it to reduce the size of the routing ta-
ble.
43.
The route is set to inactive, when a neighboring router has failed to respond to a query
about the route within three minutes.
44.
Excess LSA traffic and frequent routing table recalculations occur when a large number
of routers operate in a single OSPF area.
45.
With OSPF support of VLSM, a multiple design ensures that addresses are allocated in
an efficient manner, and summarization can be performed with different prefix lengths
throughout the network.
46.
The default router priority is 1 for purpose of participating in an OSPF DR/BDR election.

www.testkiller.com
GFI - Security & Communication tools for NT/2000: FAXmaker fax server software, Mail essentials email content checking &
anti-virus software and LANguard network security software.
http://www.gfi.com/tt.shtml
17
47.
Logical interfaces are more reliable than physical interfaces. When a subinterface’s state
changes to down, the physical interface remains up when using subinterfaces in an
NBMA topology.
48. The
show ip ospf virtual-link command is used to verify the status of an OSPF virtual
link.
49.
The hierarchical nature of OSPF allows you to separate a single large area into smaller
areas.
50.
Use BGP in the following three instances:
1.
When there are multiple connections to the Internet.
2.
When the flow of traffic entering and leaving and autonomous system
must be manipulated.
3.
When an autonomous system allows packets to transit through it to reach
other autonomous systems.
51. Do
NOT use BGP in the following three instances:
1.
When there is a single connection to the Internet.
2.
When there is a low bandwidth connection between autonomous systems.
3.
When a route selection to routes outside of your autonomous system is not
a concern.
52.
Multiple OSPF areas are connected via an OSPF ABR.
53.
Summary LAN’s will be flooded throughout the area and all area 0 routers will recalcu-
late their routing tables in response to a topology changes in area 0 if all of the frame re-
lay interfaces belong to area 0 in a multiarea OSPF network.
54.
Low memory and low CPU usage will result when the ISPs send only default routes to
the autonomous system when an autonomous system is connected via BGP to more than
one ISP.
55.
OSPF router can only route when they are in full state.
56.
By using a passive interface you can prevent all RIP routing updates from being sent
through selected RIP interfaces without using access lists.
57.
By default, FAST switching mode will allow the router to forward packets that match the
established policy with Cisco IOS release 11.2F or later.
58.
When boundary routers receive route information from both IGRP and OSPF networks,
they will select the IGRP information because of the better administrative distance.

www.testkiller.com
GFI - Security & Communication tools for NT/2000: FAXmaker fax server software, Mail essentials email content checking &
anti-virus software and LANguard network security software.
http://www.gfi.com/tt.shtml
18
59.
The following routing protocols support multiple link network layer routed protocols:
1. OSPF
2. EIGRP
3. RIPv.2
60.
A router running BGP has one table that contains BGP information received from and
sent to other routers and another table that contains IP routing information.
61.
BGP peers are also known as neighbors.
62. Use
the
clear ip bgp * command to reset all BGP sessions on a router.
63.
You can perform route summarization on an EIGRP network manually at any interface
within the network.
64.
If you are configuring the static route on a router and you want to configure it so that if
the interface associated with route goes down it will still remain in the routing table, you
must use the permanent IP route command parameter.
65.
Three characteristics of distance vector routing:
1.
Utilized by RIP and IGRP.
2.
It is the simplest routing protocol to configure.
3.
It sends periodic updates even when no network change has occurred.
66.
When you have an autonomous system that is connected via BGP to more than one ISP,
the ISP will send only default routes into the autonomous system. The path leading to the
router with the lowest BGP router ID will be used by non BGP routers as the best path to
any external address.
67. Use
the
router eigrp <autonomous system-number> command if you want to enable
EIGRP and define the autonomous system.
68.
A router on the Ethernet will update its routing table and forward the updated table to all
other routers in the network when it learns of a link state change.
69. The router ospf <process ID> <network address> <wildcard mask> <area ID>
command is mandatory to configure OSPF.
70. The
no ip forward-protocol udp 49 command is used to configure a router to prevent
TACACS UDP port 49 requests from being forwarded by the router.

www.testkiller.com
GFI - Security & Communication tools for NT/2000: FAXmaker fax server software, Mail essentials email content checking &
anti-virus software and LANguard network security software.
http://www.gfi.com/tt.shtml
19
71.
Configuring redistribution between dissimilar routing protocols when there is more than
one traffic path connecting the domains can confuse the router in the network and should
be avoided. Changing the default administrative distance and establishing large default
metric can establish a large path through the internetwork.
72.
When configuring redistribution to advertise RIP routes into EIGRP on a boundary router
you need to specify a seed metric with the default-metric command. The metric being
specified should be default-metric bandwidth delay reliability load.
73.
During route filtering, routes to be filtered are selected using the standard access list.
74.
Where you have configured redistribution between RIP and OSPF, use the show ip route
command to verify that redistribution is operating correctly on a network .
75.
To have complete topology awareness, when route distribution is required for two routing
domains with dissimilar metric structures, the routing domains should only interconnect
at the routers where the distribution is configured. Routes from one domain are assigned
a seed metric to indicate their reachability prior to being injected into the other domain.
76.
A Classful routing protocol does not carry the subnet mask within routing updates. How-
ever, Classless routing protocols use the subnet mask for each network in their routing
updates.
77.
Route maps can be defined either by name or by number. Once a match condition oc-
curs, and the corresponding set of condition has been applied, execution of the route map
is terminated.
78.
When a router can learn the network topology using both RIP and IGRP, the IGRP routes
will be placed in the routing table because they have smaller administrative distance.

www.testkiller.com
GFI - Security & Communication tools for NT/2000: FAXmaker fax server software, Mail essentials email content checking &
anti-virus software and LANguard network security software.
http://www.gfi.com/tt.shtml
20
Building Scalable Cisco Networks (BSCN)
Practice Questions
1.
You are configuring redistribution to advertise EIGRP routes into OSPF on a
boundary router. Given the following configuration, what is the function of the “20”
parameter in the redistribute command?
Router OSPF 76
Redistribute EIGRP 300 metric 20 subnets.
A: It places a metric cost of 20 and subnets to be included in each OSPF route adver-
tisement.
2.
Given the following router R3 configuration command, which three statements are
true?
Router OSPF 110
Network 192.168.32.0 0.0.0.255 area 2
Network 192.168.33.0 0.0.0.255 area 0
Area 2 stub no-summary
Area 2 default-cost 10
A: Area 2 is a totally stubby area.
R3 adds 10 to the internal cost when it gets the default route in to the stub area.
Router 2 non-ABR routes will contain only intra-area routing information and a de-
fault route.
3.
Router R1 uses a subnet mask 255.255.255.0 and sits on the boundary of area 0 and
area 1. Given the following router configuration, which three statements are true?
router OSPF 76
network 172.12.32.0 0.0.15.255 area 1
network 172.12.96.0 0.0.15.255 area 0
Area 0 range 172.12.96.0 255.255.224.0
Area 1 range 172.12.32.0 255.255.224.0
A: An interface on this router with IP address 172.12.32.124 is in area 1.
All networks within the range of 172.12.32.0 to 172.12.63.0 will be summarized
from area 1 into area 0.
Area 1 can act as a stub or transit area for routes including networks in the range
172.12.32.0 to 255.255.224.0.
4.
Given the following router configuration, which three statements are true?

www.testkiller.com
GFI - Security & Communication tools for NT/2000: FAXmaker fax server software, Mail essentials email content checking &
anti-virus software and LANguard network security software.
http://www.gfi.com/tt.shtml
21
Router OSPF 76
Network 172.22.23.34 0.0.0.0 area 1
Network 172.18.0.0 0.0.255.255 area 0
A: This is an area border router.
This area connects area 1 to backbone.
Any router interface with an address of 172.18.x.x is in area 0.
5.
Given the route summarization entry 192.168.16.0/20, how many class C addresses
can be summarized?
A: 16
6.
Given the following configuration, which two statements are true?
interface Ethernet 0.
ip address 172.16.80.77 255.255.255.0
ip helper-address 172.16.90.255
A: BOOTP request on the interface Ethernet 0 will be forwarded to network
172.16.90.0.
NetBIOS broadcasts from 172.16.80.0 will be sent as directed broadcasts to net-
work 172.16.90.0.
7.
Given the following configuration commands, which two statements are true?
router EIGRP 110.
network 172.16.0.0.
network 3.0.0.0.
A: Line 1 defines EIGRP as an IP routing process.
Line 2 causes all interfaces connected to network 172.16.0.0 to send EIGRP up-
dates to other EIGRP routers.
8.
You have configured policy based routing on serial interface 0. Given the following
configuration, which statement about a package arriving on serial 0 is most correct?
Interface serial 0
IP policy route-map demo
Route-map demo permit 10
Mach IP address 4
Set interface serial 2 serial 3
Access list 4 permit 10.3.3.2 0.0.0.0
www.testkiller.com
GFI - Security & Communication tools for NT/2000: FAXmaker fax server software, Mail essentials email content checking &
anti-virus software and LANguard network security software.
http://www.gfi.com/tt.shtml
22
A: If the packet was sourced from 10.3.3.2 it will be routed out interface serial 2 and
interface serial 3 in a load sharing fashion.
9.
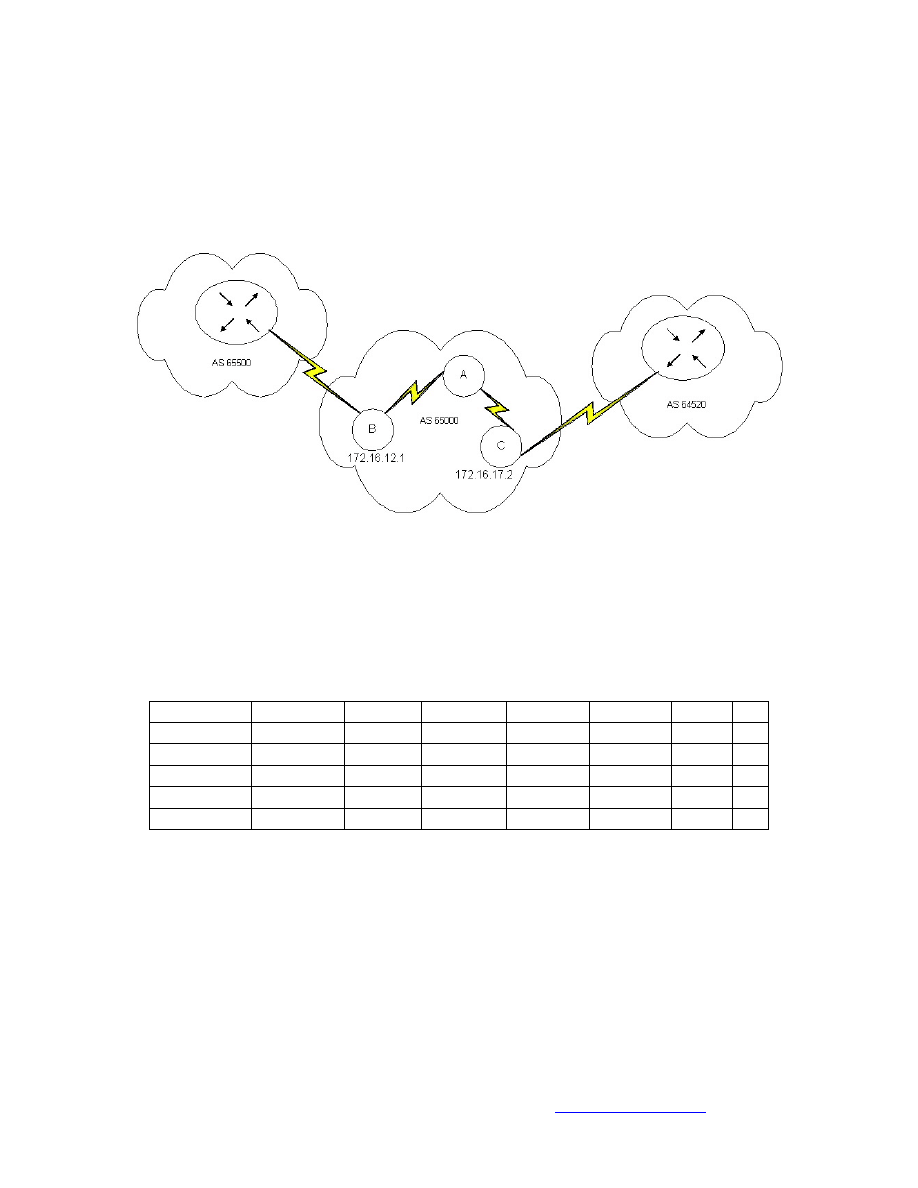
You want to configure router A as a BGP route reflector and router B as its client.
Which three commands are necessary on router A?
A: router bgp 65000
neighbor 172.16.12.1 remote-as 65000
neighbor 172.16.12.1 route-reflector-client
10.
Given the following partial information from the output of a BGP command on
router A, what next HOP address will router A use when it sends data to network
172.20.0.0?
Network
Next HOP Metric
Locprf
Weight
Patch
172.20.0.0 10.10.10.2
100
65250
65000 I
10.10.20.2 0
120
65200
65000 I
10.10.30.2
0
130
65000
I
10.10.40.2
0
140
65000
I
10.10.50.2 0
150
65300
65000 I
A: 10.10.50.2
11.
Which command must be redistributed for Ethernet 1 if you want the route 10.1.1.0
advertised?
A: ip route 10.1.1.0 255.255.255.0 interface e1
12.
Given the following router A configuration, what are two effects of the configura-
tion on router A?

www.testkiller.com
GFI - Security & Communication tools for NT/2000: FAXmaker fax server software, Mail essentials email content checking &
anti-virus software and LANguard network security software.
http://www.gfi.com/tt.shtml
23
Router BGP 65000
Network 10.0.0.0
Neighbor 172.17.1.1 remote-AS 65000
A: Line three identifies a peer router to router A.
The 65000 in line one identifies the AS that router A is in.
13.
Which two addresses can be summarized by the address 172.30.16.0/20?
A: 172.30.17.0/24
172.30.31.0/24
14.
The 172.20.0.0 had an 8-bit subnet mask extension applied to create all of its sub-
nets. One unused subnet is being used to create several additional subnets in sup-
port of a WAN deployment effort. Which subnet mask should be used to support
two host addresses on WAN segment?
A: 255.255.255.252

www.testkiller.com
GFI - Security & Communication tools for NT/2000: FAXmaker fax server software, Mail essentials email content checking &
anti-virus software and LANguard network security software.
http://www.gfi.com/tt.shtml
24
Index
advertisements....................................... 1, 13
Area Border Router..................................... 6
ASBR .......................................................... 6
autonomous system..... 7, 8, 9, 14, 15, 17, 18
Autonomous System Boundary Router ...... 6
Backbone area............................................. 6
Backbone Router......................................... 6
bandwidth............ 1, 4, 6, 7, 8, 15, 16, 17, 19
BDR ...................................................... 4, 16
BGP......... 8, 9, 10, 13, 14, 15, 17, 18, 22, 23
Border Gateway Protocol............................ 8
Broadcast................................................. 4, 5
CIDR ....................................................... 2, 3
Classful routing..................................... 1, 19
Classless Interdomain Routing ................... 2
Classless routing ................................... 1, 19
convergence .............................. 1, 2, 4, 6, 10
Discretionary Attributes.............................. 9
distance vector .............................. 1, 3, 6, 18
DR ......................................................... 4, 16
EGP ............................................................. 8
EIGRP ....... 1, 6, 7, 14, 15, 16, 18, 19, 20, 21
Exterior Gateway Protocol.......................... 8
frame relay ............................................ 7, 17
global addresses .......................................... 3
Hello Packet ................................................ 4
hierarchical addressing.......................... 2, 16
IBGP ......................................... 9, 10, 14, 15
IGP .................................................... 8, 9, 15
IGRP ......................................... 1, 17, 18, 19
interface... 3, 7, 13, 15, 16, 17, 18, 20, 21, 22
Interior Gateway Protocol........................... 8
Internal Router ............................................ 6
Internet .............................................. 2, 8, 17
IP address.......................... 2, 3, 4, 13, 20, 21
ip numbered............................................... 3
link-state.......................................... 3, 4, 5, 6
Load balancing............................................ 7
Load sharing.............................................. 10
LSA ......................................................... 2, 5
Mandatory Attributes.................................. 9
maximum transmission unit........................ 1
meshed network .......................................... 5
metric .................................. 1, 15, 19, 20, 22
multicast.............................................. 1, 2, 4
multipoint...................................... 4, 5, 7, 16
NAT ........................................................ 2, 3
NBMA............................... 4, 5, 7, 15, 16, 17
network address .................................... 2, 18
Network Address Translation ................. 2, 3
nonbroadcast ............................................... 5
Nonbroadcast multiaccess........................... 4
Nontransitive Attribute ............................... 9
Not-so-stubby area ...................................... 6
OSPF .... 2, 3, 4, 5, 13, 14, 15, 16, 17, 18, 19,
20, 21
OSPF Areas................................................. 5
point-to-point ................................ 4, 5, 7, 13
policy based routing............................ 10, 21
policy-based routing ................................... 8
prefix lists.................................................. 10
protocol ......................... 1, 3, 6, 8, 15, 18, 19
redistribution............................. 3, 10, 19, 20
RFC ............................................................. 5
RIP ........................................ 1, 3, 17, 18, 19
RIPv1 .......................................................... 1
route distribution ................................ 10, 19
route filtering ........................................ 8, 19
Route reflectors......................................... 10
route summarization.... 2, 3, 6, 13, 16, 18, 21
Route Summarization.............................. 2, 6
Routing Information Protocol..................... 3
routing policy.............................................. 8
Routing table............................................... 2
Server farm.................................................. 3
shortest path first......................................... 5
SPF.............................................................. 5
split horizon .............................................. 10
Standard area............................................... 6
Stub ............................................................. 4
Stub area...................................................... 6
subinterface ................................................. 7

www.testkiller.com
GFI - Security & Communication tools for NT/2000: FAXmaker fax server software, Mail essentials email content checking &
anti-virus software and LANguard network security software.
http://www.gfi.com/tt.shtml
25
subnet masks ..................... 1, 2, 4, 13, 15, 16
synchronization....................................... 4, 9
TCP/IP......................................................... 1
topologies.................................................... 4
topology ........................ 1, 4, 5, 7, 16, 17, 19
Topology Table........................................... 7
Totally stubby area...................................... 6
Transitive Attribute..................................... 9
Unnumbered................................................ 3
Variable Length Subnet Masks................... 2
VLSMs.............................................. 2, 4, 16
WAN ......................................... 7, 15, 16, 23
well-known attribute ................................... 8
Wyszukiwarka
Podobne podstrony:
więcej podobnych podstron